 Why would you prefer agentless approach? First of all is performance and second is seamless integration. No one likes installing new Agent. There is always this discussion if it is secure enough, fast enough and does not consume too much performance to run. If machine is highly utilized then agent also requires more performance to send more information. Complicated ? No, if You use agentless Windows Event Log subscription. Our Event Collector is free of listed problems: there is not agent, subscription is native for Windows and all communication is encrypted.
Why would you prefer agentless approach? First of all is performance and second is seamless integration. No one likes installing new Agent. There is always this discussion if it is secure enough, fast enough and does not consume too much performance to run. If machine is highly utilized then agent also requires more performance to send more information. Complicated ? No, if You use agentless Windows Event Log subscription. Our Event Collector is free of listed problems: there is not agent, subscription is native for Windows and all communication is encrypted.
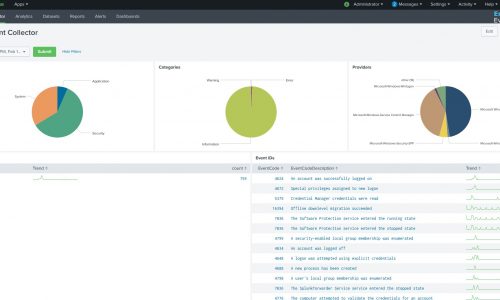
Splunk application
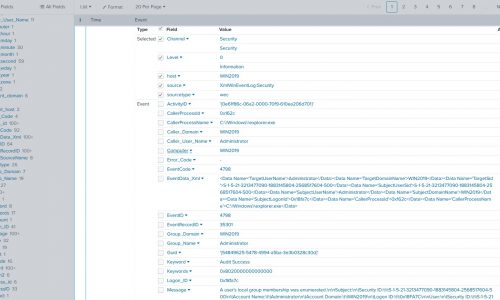
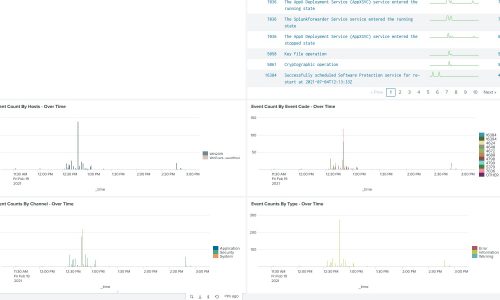
Energy Event Collector is unique and efficient software which allows you to receive Windows event logs on Linux collector. We are using native Windows mechanism for sending logs remotely by setting Windows Event Forwarding.
 Is Your Splunk running on Linux ? With Energy Event Collector You can directly subscribe to Windows Event Forwarding service from Your Linux box. We support output using xml, syslog and syslog-tls protocol both over network and using files.
Is Your Splunk running on Linux ? With Energy Event Collector You can directly subscribe to Windows Event Forwarding service from Your Linux box. We support output using xml, syslog and syslog-tls protocol both over network and using files.
If you are using Splunk Enterprise Security we have great news for You. Energy Event Collector supports security information from Windows operating system. For best results use Energy Event Collector with dedicated Splunk APP which allow you to align with existing data models in Splunk.